Internet connections Business/Domestic
The main differences between domestic (home) internet and business-grade internet revolve around performance, reliability, service quality, support, and cost. Here are the key distinctions: 1.
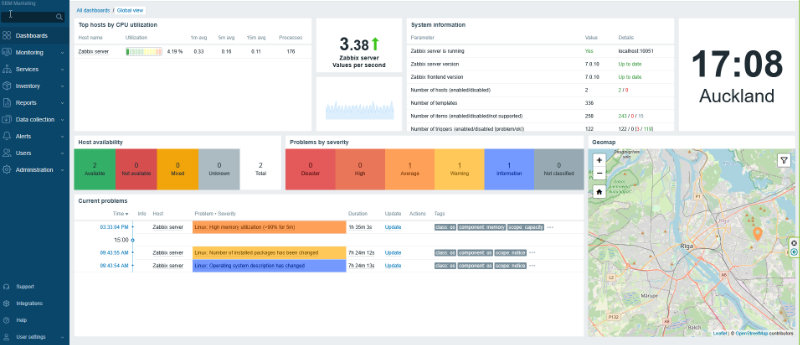
Continuous Monitoring: The Foundation of Effective Cybersecurity
In an era where cyber threats are growing in sophistication and frequency, organizations must adopt a proactive approach to cybersecurity. One of the most critical components of a strong security posture is continuous monitoring. Rather than reacting to breaches after they occur, continuous monitoring ensures that threats are identified, assessed, and mitigated in real time. This proactive approach significantly reduces the risk of damage and data loss while enhancing an organization’s ability to respond swiftly to security incidents.
Continuous monitoring in cybersecurity refers to the ongoing collection, analysis, and response to security-related data. It involves the use of automated tools, machine learning, and human oversight to detect anomalies, unauthorized activities, and vulnerabilities before they escalate into full-scale breaches. Unlike traditional security measures, which often rely on periodic audits and assessments, continuous monitoring provides a real-time view of an organization’s security posture.
This approach encompasses multiple layers, including network traffic analysis, endpoint security, log management, user behavior analytics, and compliance tracking. By leveraging these components, organizations can maintain visibility into their IT infrastructure and respond to threats before they cause significant harm.
Early Threat Detection
Cyberattacks often begin with small, seemingly insignificant actions—such as unauthorized access attempts or minor deviations in user behavior. Continuous monitoring enables security teams to detect these early warning signs and prevent potential breaches before they escalate.
Real-Time Response and Mitigation
The ability to identify and react to threats in real time is crucial for minimizing damage. Continuous monitoring ensures that security teams receive immediate alerts when suspicious activity is detected, allowing them to take swift corrective actions.
Risk Management and Compliance
Organizations are often required to comply with industry standards and regulations such as GDPR, HIPAA, and ISO 27001. Continuous monitoring helps businesses maintain compliance by providing an ongoing assessment of their security posture and identifying areas that require improvement.
Reducing Attack Dwell Time
Attack dwell time refers to the duration a cyber threat remains undetected within a system. The longer a hacker remains undetected, the more damage they can cause. Continuous monitoring significantly reduces dwell time by enabling early detection and swift response to security incidents.
Enhancing Incident Response Capabilities
An effective cybersecurity strategy includes a well-defined incident response plan. Continuous monitoring provides security teams with valuable insights into attack patterns and vulnerabilities, allowing them to refine their response strategies and improve overall resilience.
To implement a robust continuous monitoring strategy, organizations should integrate the following key components:
Security Information and Event Management (SIEM): SIEM solutions collect and analyze log data from various sources, providing real-time insights into potential security threats.
Endpoint Detection and Response (EDR): EDR tools monitor endpoints such as laptops, servers, and mobile devices to detect and respond to suspicious activity.
Intrusion Detection and Prevention Systems (IDPS): These systems monitor network traffic for signs of malicious activity and take preventive actions to block threats.
User and Entity Behavior Analytics (UEBA): By analyzing user behavior patterns, UEBA solutions can detect anomalies that indicate potential security breaches.
Automated Threat Intelligence: Integrating external threat intelligence feeds into monitoring systems helps organizations stay ahead of emerging threats.
With the rise of artificial intelligence and machine learning, cybersecurity monitoring is becoming more sophisticated. AI-driven security tools can analyze vast amounts of data, identify patterns, and predict potential threats before they occur. Additionally, automation is playing a crucial role in enhancing the efficiency of security operations, reducing human error, and accelerating response times.
As cyber threats continue to evolve, organizations must prioritize continuous monitoring as the first and most essential step in their cybersecurity strategy. By investing in advanced monitoring tools and processes, businesses can ensure the safety of their digital assets, maintain compliance, and build a resilient security framework for the future.
In today’s digital landscape, where cyber threats are an ever-present danger, continuous monitoring is not just an option—it is a necessity. Organizations that embrace proactive monitoring can stay ahead of threats, protect sensitive data, and maintain trust with customers and stakeholders. By making continuous monitoring the foundation of cybersecurity, businesses can create a robust defense against the ever-changing threat landscape and ensure long-term security success.
The main differences between domestic (home) internet and business-grade internet revolve around performance, reliability, service quality, support, and cost. Here are the key distinctions: 1.
FireWalls Explained A firewall for a small business serves as a barrier between your internal network and the outside world, typically the internet. It acts